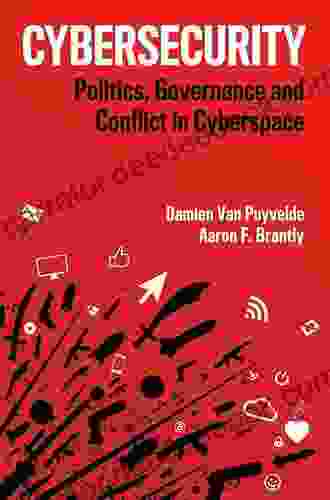
Cybersecurity Politics, Governance, and Conflict in Cyberspace: A Comprehensive Analysis

In the modern technological age, cyberspace has emerged as a vital domain that transcends geographical boundaries and has profound implications for national and global security. As the world becomes increasingly interconnected and dependent on digital infrastructure, the challenges and opportunities of cybersecurity have become more apparent.
4.5 out of 5
| Language | : | English |
| File size | : | 3862 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 219 pages |
| Lending | : | Enabled |
This article provides a comprehensive analysis of cybersecurity politics, governance, and conflict in cyberspace. It explores the complex geopolitical landscape, international cooperation, and legal frameworks governing this critical domain. By understanding these dynamics, we can better address the challenges and ensure a secure and stable cyberspace.
Cybersecurity Politics: A Complex Geopolitical Landscape
Cyberspace is not a separate realm but rather an extension of the physical world, reflecting the geopolitical interests and tensions between nations. States seek to protect their national interests, critical infrastructure, and digital sovereignty in cyberspace. However, the decentralized and global nature of the internet presents unique challenges for traditional notions of sovereignty and control.
Major powers, such as the United States, China, Russia, and the United Kingdom, have emerged as key players in cybersecurity politics. They possess significant cyber capabilities and are actively engaged in developing and implementing cybersecurity strategies. These states often pursue conflicting agendas, leading to tensions and competition in cyberspace.
The geopolitical landscape of cyberspace is further complicated by the involvement of non-state actors, such as criminal organizations, hacktivist groups, and terrorist organizations. These groups can launch cyber attacks for various reasons, ranging from financial gain to political protest and intimidation. Their activities can disrupt critical infrastructure, steal sensitive information, and undermine public trust in digital technologies.
International Cooperation in Cybersecurity Governance
Recognizing the global nature of cybersecurity threats and the need for collective action, nations have engaged in various international cooperation initiatives to address these challenges. The United Nations has played a leading role in promoting dialogue and cooperation on cybersecurity issues.
In 2013, the UN General Assembly adopted a resolution on "The role of the United Nations in promoting an international cybersecurity agenda." This resolution called for the establishment of a UN Group of Governmental Experts (GGE) on cybersecurity to develop norms and guidelines for responsible state behavior in cyberspace.
The GGE released two reports in 2015 and 2019, which outlined a set of norms and principles for responsible state behavior in cyberspace. These norms include the following:
- States should refrain from using ICTs for malicious purposes.
- States should respect the sovereignty and territorial integrity of other states in cyberspace.
- States should cooperate to prevent and mitigate cyberattacks.
- States should protect critical infrastructure from cyber threats.
- States should promote the peaceful and responsible use of ICTs.
In addition to the UN, other international organizations and initiatives have been established to promote cooperation on cybersecurity. These include the Organization for Security and Co-operation in Europe (OSCE),the North Atlantic Treaty Organization (NATO),and the Shanghai Cooperation Organization (SCO).
Cyber Conflict and the Legal Framework
Despite international cooperation efforts, cyber conflict remains a growing concern. States may engage in cyber operations against each other for various reasons, including espionage, sabotage, and warfare.
The legal framework governing cyber conflict is still evolving. There is no international treaty that specifically addresses the use of force in cyberspace. However, some principles of international law, such as the UN Charter and the Geneva Conventions, may be applicable to cyber operations.
In addition, several national laws have been enacted to address cybercrime and cyber warfare. However, these laws vary from country to country, and there is no universally accepted definition of what constitutes a "cyberattack."
The Challenges of Cybersecurity Politics and Governance
Addressing the challenges of cybersecurity politics and governance requires a multifaceted approach that involves technological, legal, and diplomatic measures. Some of the key challenges include:
- Attribution: It can be difficult to determine the source of a cyberattack, making it challenging to hold perpetrators accountable.
- Deterrence: Developing effective deterrence strategies against cyberattacks is complex, especially when dealing with non-state actors.
- International cooperation: Building trust and cooperation among nations on cybersecurity issues is essential but can be hindered by geopolitical tensions.
- Evolution of technology: The rapid evolution of technology poses challenges for policymakers and law enforcement agencies to keep pace with the latest threats.
Cybersecurity politics, governance, and conflict in cyberspace are complex and evolving issues that impact the global community. Understanding the geopolitical dynamics, the challenges of international cooperation, and the legal frameworks governing cyberspace is crucial for addressing these challenges effectively.
By fostering dialogue, collaboration, and a commitment to responsible behavior in cyberspace, we can mitigate risks, maintain stability, and create a secure and prosperous digital world for the future.
4.5 out of 5
| Language | : | English |
| File size | : | 3862 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 219 pages |
| Lending | : | Enabled |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Paperback
Paperback E-book
E-book Paragraph
Paragraph Bookmark
Bookmark Bibliography
Bibliography Foreword
Foreword Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Codex
Codex Tome
Tome Classics
Classics Library card
Library card Narrative
Narrative Autobiography
Autobiography Memoir
Memoir Thesaurus
Thesaurus Narrator
Narrator Borrowing
Borrowing Archives
Archives Study
Study Lending
Lending Reserve
Reserve Rare Books
Rare Books Special Collections
Special Collections Interlibrary
Interlibrary Literacy
Literacy Thesis
Thesis Dissertation
Dissertation Storytelling
Storytelling Book Club
Book Club Theory
Theory Textbooks
Textbooks Erik Daniel Shein
Erik Daniel Shein Nigel Dennis
Nigel Dennis Stefan Einhorn
Stefan Einhorn Ian Yeoman
Ian Yeoman Eileen Riley
Eileen Riley Ruth Brown
Ruth Brown Marc Morial
Marc Morial Allison Edwards
Allison Edwards Shep Hyken
Shep Hyken Mark Batterbury
Mark Batterbury Weatherspoon
Weatherspoon Sarah Davids
Sarah Davids Jean Valentine
Jean Valentine Kevin Woyce
Kevin Woyce Roseann Meehan Kermes
Roseann Meehan Kermes Stephen J Blank
Stephen J Blank George Pintar
George Pintar Frank M Young
Frank M Young Daniel Hall
Daniel Hall John Zilcosky
John Zilcosky
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Gabriel Garcia MarquezThe Ultimate Step-by-Step System to Elevate Student Motivation in Your...
Gabriel Garcia MarquezThe Ultimate Step-by-Step System to Elevate Student Motivation in Your...
 Patrick HayesDelving into the Timeless Melodies of the Old Time Gospel Songbook: A Musical...
Patrick HayesDelving into the Timeless Melodies of the Old Time Gospel Songbook: A Musical... Bryan GrayFollow ·7.3k
Bryan GrayFollow ·7.3k Jedidiah HayesFollow ·16.2k
Jedidiah HayesFollow ·16.2k Derrick HughesFollow ·10.2k
Derrick HughesFollow ·10.2k Raymond ParkerFollow ·16.6k
Raymond ParkerFollow ·16.6k Houston PowellFollow ·14.5k
Houston PowellFollow ·14.5k Quincy WardFollow ·8.7k
Quincy WardFollow ·8.7k Roberto BolañoFollow ·14.4k
Roberto BolañoFollow ·14.4k Virginia WoolfFollow ·9k
Virginia WoolfFollow ·9k
 Abe Mitchell
Abe MitchellUnveiling the Urban Cheating Rich System: A Comprehensive...
In today's complex and ever-evolving urban...
 Preston Simmons
Preston SimmonsSelection, Processing, and Care of Reeds: A Comprehensive...
Reeds are essential...
 Rob Foster
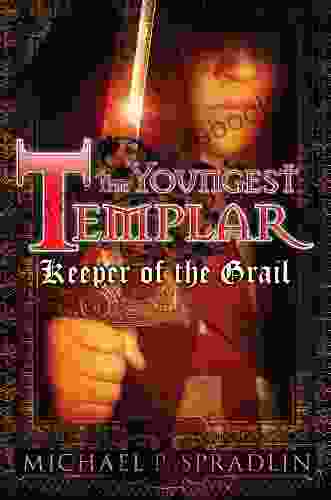
Rob FosterKeeper of the Grail: The Youngest Templar
Prologue: A Sacred...
4.5 out of 5
| Language | : | English |
| File size | : | 3862 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 219 pages |
| Lending | : | Enabled |